Every week, a corporate client shows me a newly installed magnetic lock and claims their perimeter is secure. They are wrong. A lock is passive. It holds a door closed. It does not think. It does not care if the person holding the keycard is your CEO or a fired contractor who stole it from a desk. So, what is access control? It is not a hardware installation. Real access control security is the active, continuous filtration of physical threats. It is a strict operational protocol. You need the right personnel enforcing rigid rules at the exact right time. A high-definition camera just films the disaster for the insurance claim. An active protocol prevents the breach from happening. Security is not an electronic state. It is an ongoing physical action.
The Three Pillars of Access Management
Forget the vendor brochures. Electronics fail. Networks go down. Real access management systems boil down to three brutal operational questions. This triad forms the absolute baseline of functional physical security. If you fail one, your perimeter is compromised.
- Identification: Who is standing at the choke point? Not “whose card was swiped.” Who is the physical person? This requires visual verification. A biometric scanner provides data. A trained operator confirms reality.
- Authorization: Do they belong in this exact zone at this exact minute? A valid ID badge is not a universal pass. The CFO is authorized in the boardroom. He is not authorized in the main server rack at 3 AM. Clearances must be heavily compartmentalized.
- Accountability: We track the physical footprint. No anonymous entries. Ever. If a secure zone is breached, we know exactly who crossed the line and at what millisecond. You cannot enforce rules if you cannot audit the movement.
Why Technology Fails Without People
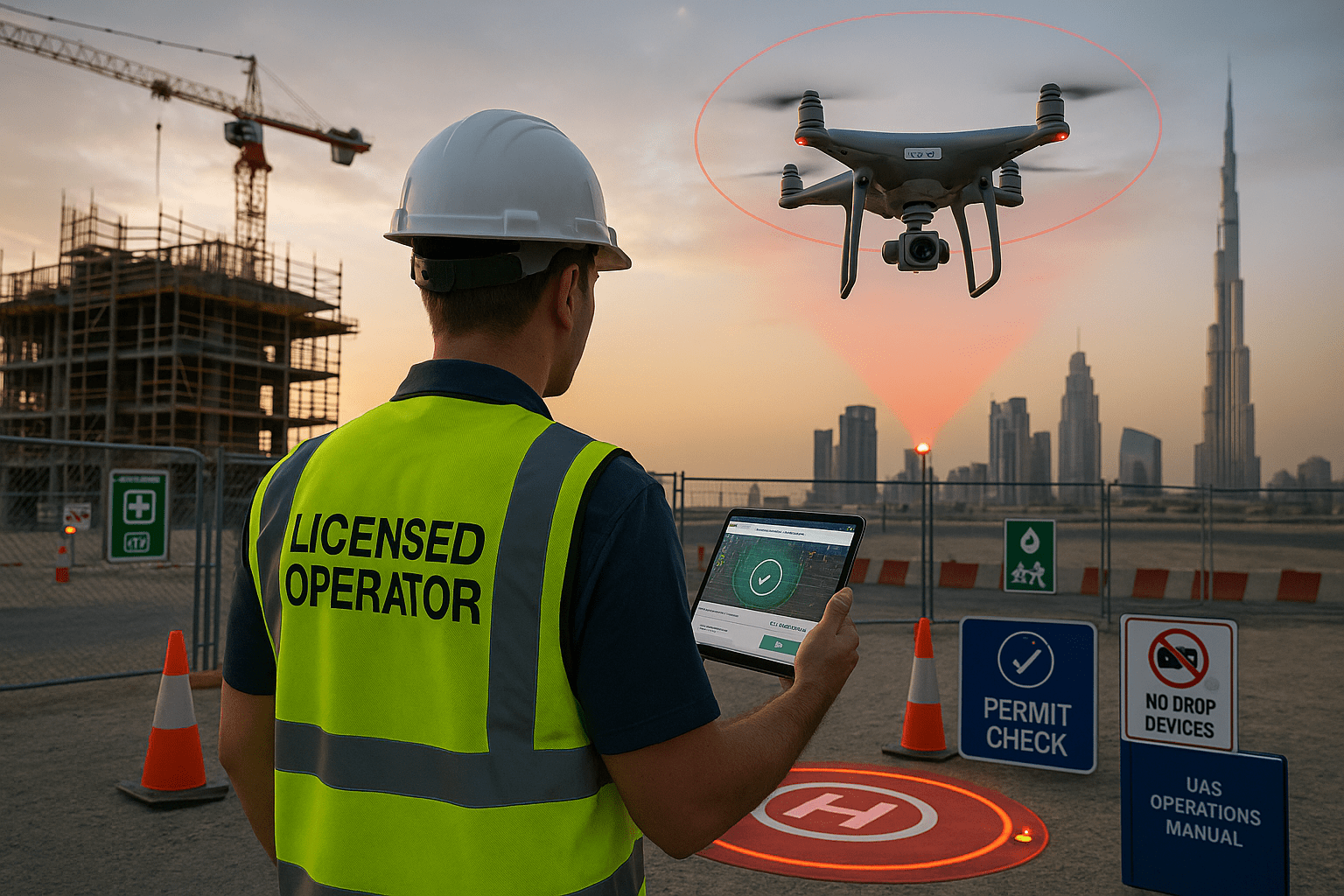
Hardware is blind. I see the same vulnerability on every site audit. A cleared employee swipes their badge at the main entrance. They hold the door open out of basic politeness for a stranger carrying a box of coffees. The access software registers one authorized entry. It completely ignores the unauthorized body walking right past the $50,000 scanner. A magnetic lock will not jump off the wall to stop them.
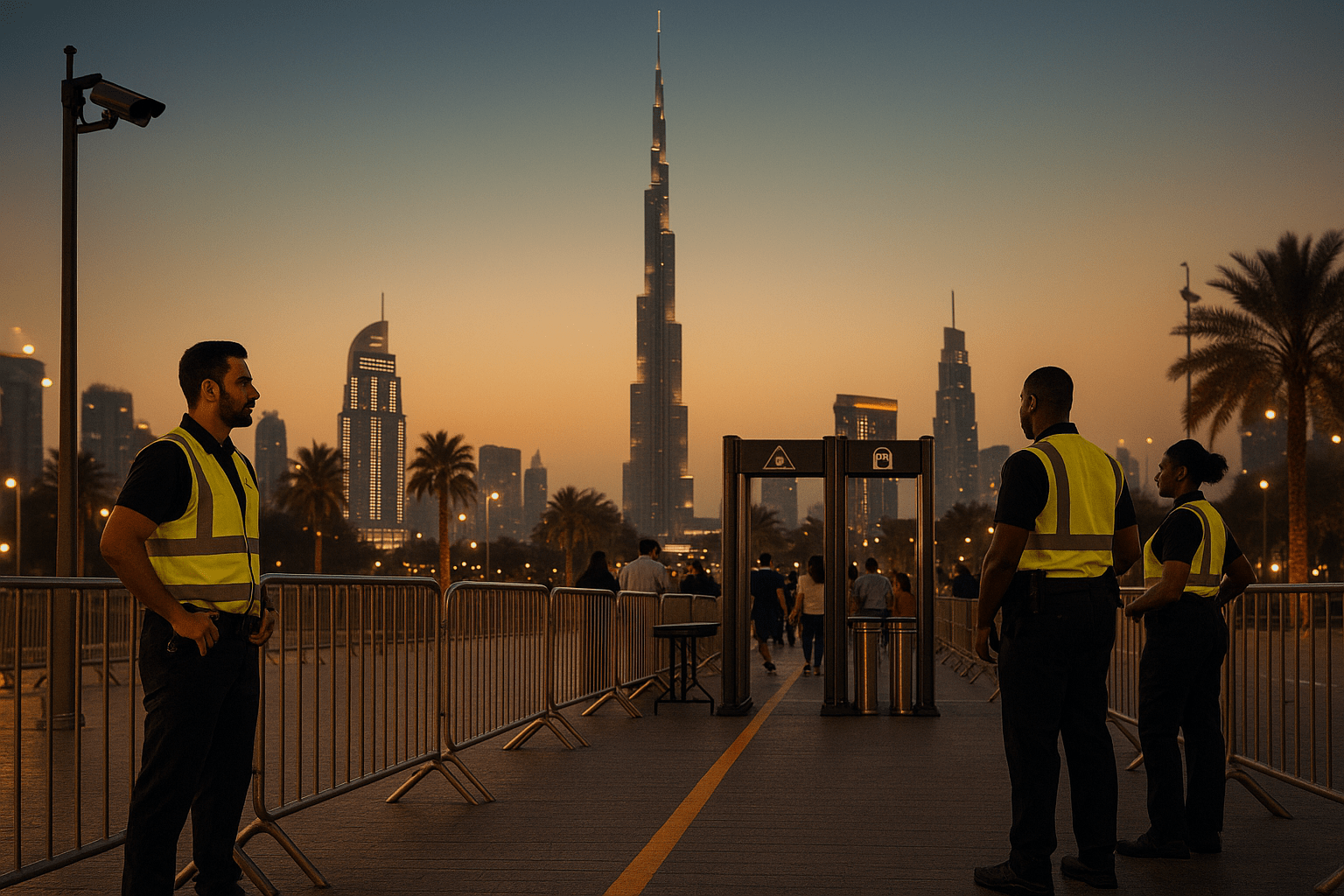
This is why high-end door security Dubai relies entirely on human operators. Technology issues digital alerts. Professional guards neutralize physical threats. Utilizing specialized porter services puts a trained set of eyes on your choke points. A human reads the environment. They spot the social engineering tactics that software misses. They intercept the stranger with the coffees. They step into the threshold and physically block the passage. The guard is the final barrier.
Vulnerabilities You Are Probably Ignoring
Corporate perimeters do not fail in spectacular ways. They erode through daily laziness. Management buys expensive software but ignores the physical realities of their secure entry points. Here is what is actually compromising your facility right now:
- Borrowed Credentials: Badges are constantly swapped between colleagues to save time. The system logs a manager entering the fourth floor. The manager is actually at home. The audit trail is instantly corrupted.
- Ghost Access Profiles: HR fires a vendor. IT forgets to kill the access profile in the system. You now have an angry, terminated outsider walking around with a functional master key. This is a massive insider threat.
- Unmonitored Back Doors: You secured the main lobby with turnstiles. Excellent. But your loading dock is wide open, and the delivery drivers are propping the fire exit open with a fire extinguisher. A perimeter is only as strong as its weakest, unmonitored exit.
The PSM UAE Protocol: Integrated Access Control
We do not just place bodies in uniforms at a reception desk. PSM UAE integrates tactical physical presence with your existing electronics. We deploy SIRA certified guards to own your perimeter. Our operators undergo rigid selection. Many bring years of military and police background to the corporate environment. They understand aggressive tailgating prevention. They understand crowd dynamics and behavioral profiling.

We operate on strict protocols. If a choke point is compromised, we escalate instantly. We deploy rapid response strike teams within 46 minutes. We handle daily corporate access management and large-scale, volatile Event Security. The electronics sound the alarm. Our personnel lock down the facility. We execute the protocol.
Audit Your Perimeter Today
A weak perimeter is a liability waiting to be exploited. Corporate espionage, asset theft, and data breaches start with a propped-open door. Stop relying on passive locks. Contact PSM UAE to schedule a hard, operational audit of your facility in Dubai or Abu Dhabi. Let us expose your vulnerabilities before someone else does.